
API Security
8 minutes
NIST Cybersecurity Framework
The NIST Cybersecurity framework provides organizations with a set of standards, guidelines, and practices to develop strong cybersecurity practices for managing cybersecurity risks effectively.

Muze

API Security
7 minutes
API Security Audit
An API Security Audit evaluates APIs, identifies potential risks, and strengthens the organization's defenses against security breaches and cyber-attacks.

Muze

API Security
8 minutes
Security Information and Event Management (SIEM)
SIEM aggregates and analyzes security data across an organization to detect, monitor, and respond to potential threats in real time.
Insha
API Security
7 minutes
Shift-Left Testing: Benefits and How to Implement It
Shift Level testing helps quickly identify and fix bugs by integrating testing activities earlier in the entire software development lifecycle.

Muze
API Security
3 minutes
What is API Discovery?
API Discovery helps identify, map, and manage APIs within an organization, ensuring security, performance, and seamless integration across systems.

Kruti
API Security
5 minutes
Top 10 DAST Tools
DAST tools secure web apps by identifying vulnerabilities through automated security testing.

Kruti

API Security
8 minutes
Top 10 API Security Tools in 2025
Top 10 API security tools help organizations protect their APIs from threats and vulnerabilities by offering real-time monitoring, authentication, encryption, and compliance to safeguard sensitive data and prevent unauthorized access.

Muze

API Security
8 minutes
Top 10 API Discovery Tools
API Discovery Tools help organizations automatically identify, catalog, and manage their APIs, improving efficiency and visibility across multiple applications and services.
Kruti

API Security
8 minutes
Top 10 API Security Testing Tools
10 Best API security testing tools to help organizations protect their APIs from vulnerabilities and cyberattacks.

Muze
API Security
8 minutes
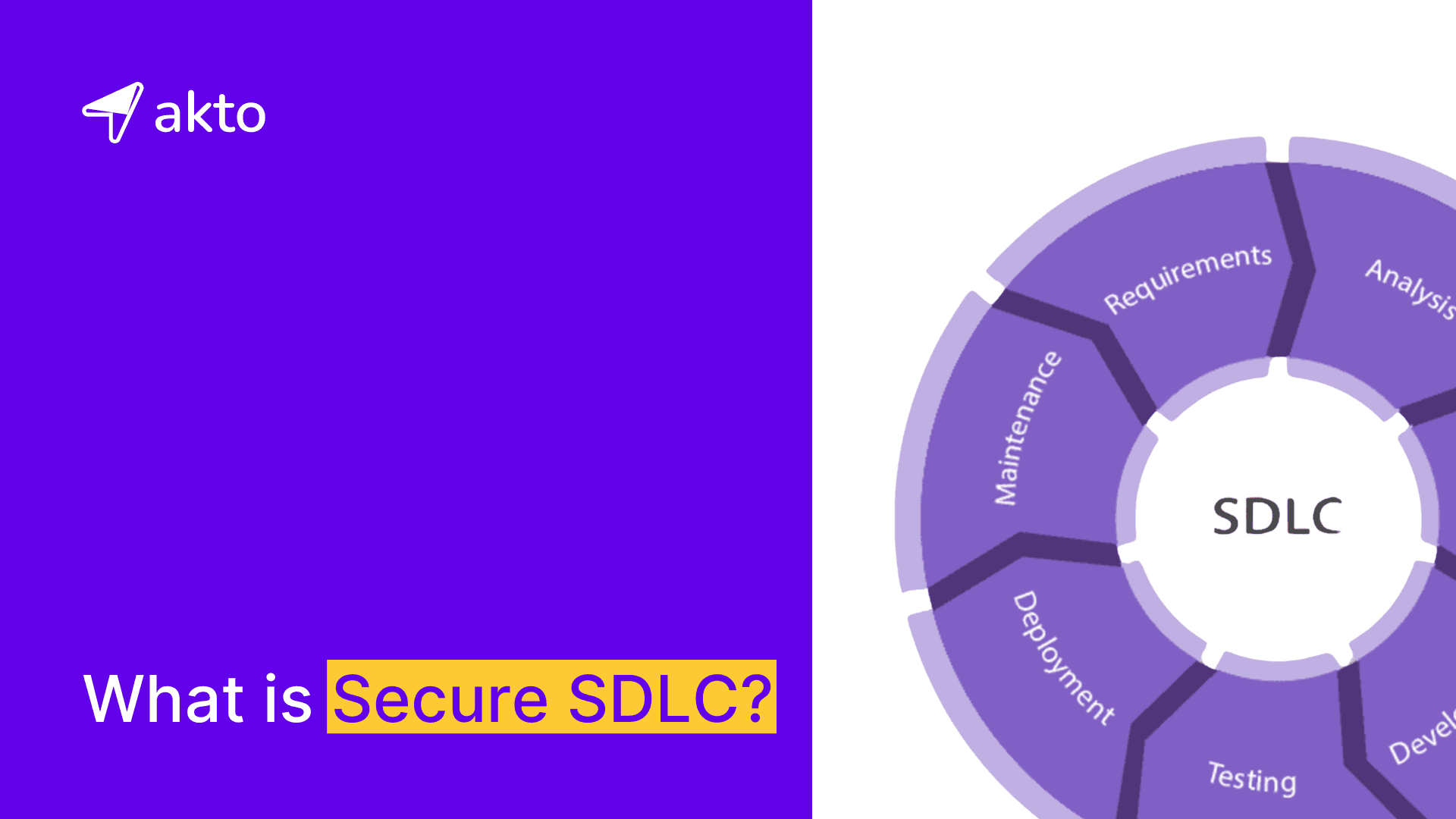
Secure SDLC (Secure Software Development Life Cycle)
The software development life cycle integrates security measures throughout the development process to address vulnerabilities and protect the organization's sensitive data.

Muze
API Security
5 minutes
How to Build an Application Security Program
An Application Security Program uses various policies, procedures, and technical measures to protect the organization's software applications from potential security risks and vulnerabilities.

Muze

API Security
6 minutes
LockBit Ransomware: Its History and How It Works
LockBit Ransomware is a malicious software that hackers use to encrypt files and threaten organizations with the deletion or leakage of the files if they do not pay the ransom.

Muze

API Security
8 Minutes
Top 10 Invicti Alternatives in 2025
In this blog, explore the top 10 Invicti Security alternatives and competitors, including key features and comparisons to help you choose the best solution.

Muzammil

API Security
8 minutes
Data Protection Policy: Key Components and Best Practices
A data protection policy comprises the rules and guidelines an organization follows to ensure compliance with data protection laws.

Muze
API Security
7 minutes
Security Champions Overview
A security champion serves as an extension of the security team and ensures that security is evenly distributed among development teams.

Muze

API Security
6 minutes
Security Debt: A Comprehensive Guide to How It Works
Security debt refers to the increase in minor issues or flaws in an organization's software system, which makes it tougher for the organization to keep its information and systems safe from hackers.

Muze
API Security
7 minutes
Security Requirement: Types, Purpose, and Importance
Security requirements illustrate the specific procedures, controls, and safeguards that protect an organization's sensitive data from cyber threats and data breaches.

Muze
API Security
8 minutes
Gartner API Security
Gartner emphasizes the importance of API security and evaluates vendors in its Magic Quadrant based on their execution ability and vision completeness.
Insha
API Security
10 minutes
Secure Coding Practices
Secure coding is the practice of writing software to prevent vulnerabilities and security threats, reducing the risk of breaches, unauthorized access, and other issues.
Insha

API Security
8 minutes
Fortify DAST: Scanning & WebInspect Setup
Fortify DAST secures your deployed web applications and services from potential vulnerabilities by simulating attacks.

Muze

API Security
8 minutes
Guide of Veracode DAST: Essentials, Documentation and Pricing
Veracode DAST simulates external attacks to check your web applications and APIs for security vulnerabilities.

Muze

API Security
10 minutes
Checkmarx DAST: How the Scan Works
Checkmarx DAST examines your live web applications and APIs for security issues by mimicking real-world attacks.

Muze
API Security
10 minutes
42Crunch Alternatives
42Crunch is an API security platform that automates auditing, testing, and protection of APIs.
Insha

API Security
8 minutes
Invicti DAST: Configuring a Scan and How Scanning Works in Invicti DAST
Invicti DAST is a tool designed to identify security vulnerabilities in websites and web applications by simulating real-world attacks.

Muze

API Security
10 minutes
Synopsys DAST or WhiteHat DAST: Integrating Synopsys DAST with CI/CD Pipelines
Synopsys DAST or WhiteHat DAST secures your running web applications from potential vulnerabilities by simulating real-world attacks.

Muze
API Security
12 minutes
Top 10 API Gateways
An API gateway manages incoming API requests and directs them based on factors such as request path, headers, and query parameters, while covering the internal structure of the application.

Muze

API Security
10 minutes
OWASP Dynamic Application Security Testing (DAST): Key Features and Limitations
OWASP DAST is a tool designed to uncover security flaws in your live application by simulating external attacks.

Muze

API Security
9 minutes
DAST Gartner: How Gartner’s Magic Quadrant for DAST Works and Its Impact
DAST Gartner protects your applications from security vulnerabilities by simulating attacks in real time.

Muze
API Security
12 minutes
What is Security Management?
Security Management is the process of protecting an organization's assets from internal, external, and cyber attacks.

Muze
API Security
7 minutes
7 Key Security Features Every Application Should Have
Explore the must-have features that ensure the application maintains availability, stability, integrity, and confidentiality while minimizing the risk of vulnerabilities and security threats.

Muze

API Security
10 minutes
Qualys DAST: The Key Features of Qualys DAST
Qualys DAST is a tool that checks running applications from outside to inspect security flaws.

Muze

API Security
9 minutes
How to Use Snyk DAST? Integrating Snyk DAST into Your CI/CD Pipeline
Snyk DAST examines your applications in real-time from outside to find possible security issues.

Muze

API Security
10 minutes
GitLab DAST: Template Setup, Authentication, and Step-by-Step Scanning Guide
GitLab DAST is a tool that simulates attacks on your web applications to protect them from potential security issues.

Muze

API Security
12 minutes
Tenable DAST: How it Works and How Organizations use It
Tenable DAST is a tool designed to protect modern applications including those reliant on javascript and AJAX frameworks from online threats.

Muze
API Security
10 minutes
What is Code Security?
Code Security helps to identify and resolve security vulnerabilities in the source code, design, and architecture of software applications.

Muze

API Security
10 minutes
Vulnerability Assessment: Key Process and Benefits
Vulnerability Assessment is the process of identifying and ranking potential security flaws in an organization's system based on their severity.

Muze
API Security
8 minutes
What is NIST 800-53? A Complete Guide to Compliance
NIST 800-53 is a framework providing security and privacy controls to safeguard sensitive information and creating a culture of security awareness in organizations.

Muze

API Security
12 minutes
Burp Suite DAST Overview: How Burp Suite Operates
Burp Suite DAST protects your web applications from security vulnerabilities by simulating the actions of a malicious attacker.

Muze

API Security
10 minutes
Top 10 Best RASP Solutions
10 Best RASP Solutions that continuously monitor software applications to Identify and protect against threats in real time.

Muze

API Security
10 minutes
Top 10 Best WAF Solutions
10 best Web Application Firewall (WAF) solutions that filter and monitor web traffic, blocking malicious hackers before they can attack.

Muze
API Security
7 minutes
What is OWASP SAMM?
OWASP SAMM (Software Assurance Maturity Model) enhances the security posture of organizations by reducing vulnerabilities and safeguarding sensitive data from cyber threats.

Muze

API Security
8 minutes
What is a Security Review? How to Conduct a Security Review?
A security review is a process that thoroughly examines the system or a software application for potential weaknesses and vulnerabilities, and improves the safety of the system.

Muze

API Security
6 minutes
Cyber Resilience Act (CRA)
The Cyber Resilience Act ensures the safety of the organization's digital world from online dangers like hackers, including threats like SQL injection and XSS.

Muze

API Security
10 minutes
GitHub DAST: Key Features and Its Use Cases
GitHub DAST protects your web applications from security vulnerabilities by simulating attacks on web applications while it is running.

Muze

API Security
10 minutes
Rapid7 DAST: Steps to Install and Configure Rapid7 DAST
Rapid7 DAST analyzes web applications to detect security vulnerabilities, helping you safeguard your apps from cyber threats and ensure robust protection.

Muze

API Security
12 minutes
ZAP DAST Overview: Installation Guide
ZAP DAST secures your web applications during runtime from security vulnerabilities by mimicking the actions of a malicious attacker.

Muze

API Security
10 minutes
PCI DSS Guidelines
PCI DSS includes a set of rules designed to ensure the safety and security of credit and debit card information, protecting it from data breaches.

Muze
API Security
6 minutes
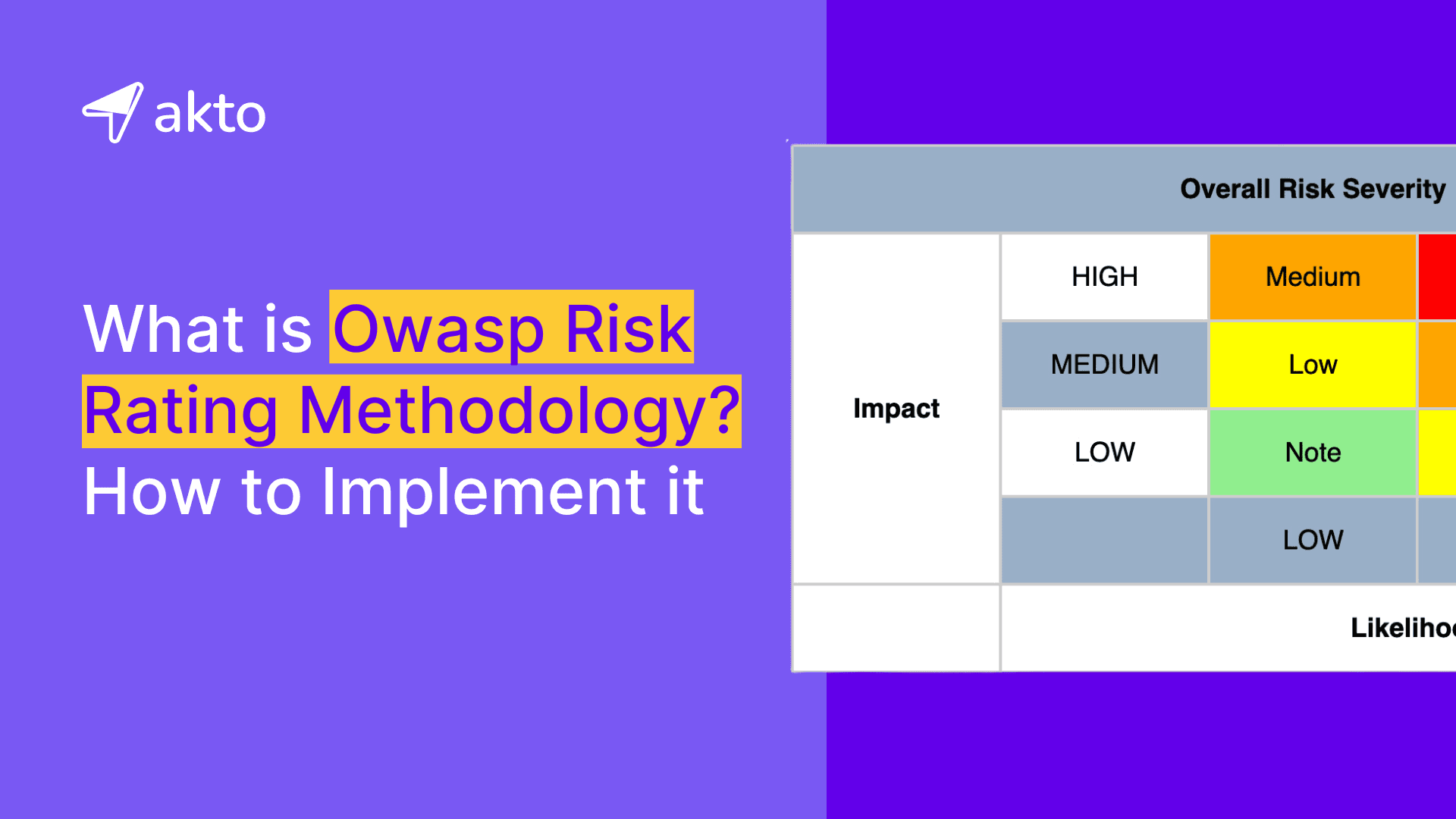
OWASP Risk Rating Methodology
The OWASP Risk Rating Methodology assigns a rating to the identified risks by considering the likelihood of the risk and its potential impact on the organization.

Muze

API Security
8 minutes
DAST Black Box Testing: Types of Black Box Testing and How it works
Black Box Testing is a methodology where the internal workings of the system under test are unknown to the tester.

Muze

API Security
9 minutes
10 Best Security Training and Courses
Explore the 10 cybersecurity training courses providing learners with essential skills on how to identify, handle and manage threats, through flexible formats and comprehensive curriculum.

Muze

API Security
10 minutes
Dynamic White Box Testing Guide - Key Features, Levels and Examples
Dynamic White Box Testing is a strategy in which the tester is aware of the internal structure of the application under test.

Muze

API Security
3 minutes
Twilio Data Breach: 33 Million Authy User Phone Numbers Exposed
Twilio's data breach exposed 33 million Authy user phone numbers because of an unauthenticated endpoint.
Insha
API Security
3 minutes
Trello Data Breach: 15 Million Email Addresses Exposed
Trello's Data Breach exposed 15 million email addresses of users due to an unsecured API.

Muze

API Security
5 mins
Prompt Injection Vulnerabilities in LLMs: An Overview of OWASP LLM01
Prompt injection in Large Language Models (LLMs) is a security attack technique where malicious instructions are inserted into a prompt, leading the LLM to unintentionally perform actions that may include revealing sensitive information, executing unauthorized actions, or manipulating its output.

Arjun

API Security
6 mins
LLM Risks: Insights & Real-World Case Studies
LLM security involves protecting AI systems like ChatGPT, Bard from potential risks such as biased outputs, malicious use and maintaining privacy in their applications.

Arjun

API Security
7 mins
Insecure Output Handling in LLMs: Insights into OWASP LLM02
This blog is about "Insecure Output Handling" that pertains to the potential risk that may arise when the content generated by an LLM is not adequately sanitized or filtered prior to being presented to the end user.

Arjun

API security
15 mins
XML injection vulnerability: Examples, cheatsheet and prevention
XML Injection is a type of attack that targets web applications that generate XML content. Attackers use malicious code to exploit vulnerabilities in XML parsers to manipulate the content of an XML document.

Medusa

API Security
6 min
Exploring the OWASP API Top 10: The Leading Security Threats of 2023
The OWASP Top 10 for API 2023 is the latest list released by the Open Web Application Security Project (OWASP). In this blog you will learn what are these top 10 API vulnerabilities and how to protect your APIs against them.

Medusa

API Security
10 mins
Top 10 API Security Best Practices you must Implement
A comprehensive guide on the top 10 API security best practices, covering authentication, encryption, testing, and vulnerability prevention.

Medusa

API Security
6 Mins
SQL Injection Cheat Sheet
A comprehensive guide to SQL Injection vulnerabilities, techniques, and examples. Learn how to exploit different databases and bypass WAF.

Medusa

API Security
10 mins
API Security in DevSecOps with Joe Gerber, VP AppSec Wells Fargo
On 18th Jan, 2024, Akto hosted a Webinar on API Security in DevSecOps with Joe Gerber, VP Appsec at Wells-Fargo.

Raaga Srinivas

API Security
6 min read
Defending Against BOLA Attacks: Testing Endpoints with Vulnerable User IDs
In this blog you will learn how to test for Broken Object Level Authorization with weak enumerable user IDs.
Jaydev Ahire

API Security
8 min read
What is Broken Object Level Authorization (BOLA)?
Broken Object level Authorization is the most critical vulnerability in OWASP Top 10 of APIs.
Jaydev Ahire

API Security
5 min read
How to Test JWT NONE Algorithm Vulnerability?
In this blog, you will learn How to test JWT NONE Algorithm vulnerability using Akto.
Jaydev Ahire

API Security
9 mins
CORS Vulnerabilities: How Attackers Exploit Cross-Origin Resource Sharing to Steal API Keys
CORS is commonly used to enable web pages to interact with APIs hosted on a different domain than the web page itself.

Medusa

API Security
8 mins
What is IDOR? Insecure direct object reference
IDOR is a type of security vulnerability that is caused by an application's failure to properly validate and authorize user input leading to unauthorized action.

Medusa

API Security
10 mins read
SQL Injection: A Comprehensive Guide to Understanding SQL Injection Risks
SQL Injection (SQLi) is a type of attack where an attacker injects malicious SQL code into a vulnerable application's database query.

Medusa

API Security
5 min read
Mass Assignment Vulnerability: How to Test Mass Assignment in APIs using Akto
This blog is about learning mass assignment vulnerability, how to find it manually, how to test for it using Akto and finally how to prevent it.

Medusa

API Security
6 mins read
How To Test BOLA by Parameter Pollution Using Akto
In 2016, a security researcher discovered a vulnerability that allowed attackers to bypass Uber's two-factor authentication system and take over accounts by exploiting BOLA via parameter pollution.

Medusa

API Security
8 mins read
BFLA: How to test Broken Function Level Authorization by Changing the HTTP Method Using Akto?
The Equifax data breach in 2017, which exposed the personal information of 143 million individuals, was a result of a vulnerability in the Apache Struts API framework and a broken functionality level authorization (BFLA) in Equifax's web application.

Medusa

API Security
10 min read
What's changed in OWASP API Security Top 10 2023 Release Candidate from 2019?
In this blog, we will compare the changes of OWASP API Security Top 10 2019 and OWASP API Security Top 10 2023 release candidate.
Jaydev Ahire

API Security
6 min read
Broken Authentication: What is Broken User Authentication (BUA)?
Broken User Authentication is one of the most critical vulnerability in OWASP Top 10 of APIs.
Jaydev Ahire

API Security
5 min read
Testing UUID Security: Preventing BOLA Exploitation on API Endpoints
This blog is about how to test for BOLA using unauthorized UUID on an API endpoint.

Jaydev Ahire
Monthly product updates in your inbox. No spam.
No spam. Ever.